blog
RSAC 2020 takeaways on defending serverless infrastructure, securing public cloud resources, and hardening multi-cloud environments.
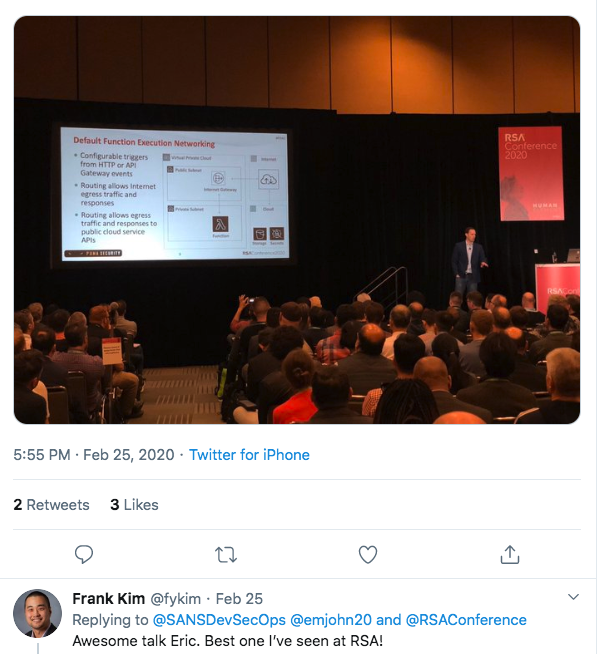
RSA 2020 (The Human Element), wrapped up in San Francisco last week. Our cloud security expert and principal SANS institute instructor, Eric Johnson was able to connect with industry leaders from around the world. The conference offered an opportunity to both learn and provide groundbreaking information on cloud security and serverless infrastructure.
Overall, here were some key takeaways from RSAC 2020:
Our technical session examined real-world scenarios that security professionals encounter defending Cloud workloads running on Serverless Infrastructure. Attendees saw a series of hands on attack techniques for exploiting serverless functions, and learned how to apply security controls defending against the attack.
The session started with insecure secrets management in Serverless. Live demonstrations showed how a vulnerability in a function can allow attackers to exfiltrate secrets from a configuration file inside the function’s execution environment. Then, how to securely store secrets in a vault protected by the cloud key management service (KMS).
Cloud resources running under the context of a role with excessive privileges have been responsible for countless breaches. Serverless is no exception. Live demonstrations showed how to extract credentials from a function’s execution environment, and used those credentials from a remote machine to gain unauthorized access to data. Attendees saw how to enforce least privilege roles and block external requests for private cloud resources.
Serverless Infrastructure is built on an ephemeral execution environment that is supposed to live for a few hundred milliseconds and then disappear. In practice, does that hold true? Live demonstrations explored how long data actually persists malware in the execution environment. We covered how to harden the execution environment to prevent data persistence and exfiltration.
Concluding the session, we discussed how serverless environments affect forensics and incident response teams. There are no images to analyze, no memory to dump. The only evidence left are audit logs. Session attendees learned how to capture key function events, build cloud dashboards, detect anomalies, and configure alerts to effectively monitor the Serverless Infrastructure.
Attendees walked away with an understanding of the common attacks and practical security controls for defending their Serverless Infrastructure.
Learned how to reverse engineer function execution environments
Detected compromised credentials
Applied function network controls
“Great talk on Defending Serverless Infrastructure in the Cloud, my favorite from yesterday!”

“Would you like to know how to defend serverless functions in AWS, GCP, or Azure? Check out this amazing talk by my fellow SANS instructor Eric Johnson.”
“Best talk I’ve seen at RSAC”
"Lock down your serverless development" - TechBeacon
![]()
Would you like to learn more about Defending Serverless Infrastructure in the Cloud? Contact us today: sales [at] pumasecurity [dot] io. Make sure to follow our social channels, @puma_scan on twitter and @puma-security-llc on linked in.
Eric Johnson’s experience includes application security automation, cloud security reviews, static source code analysis, penetration testing, SDLC consulting, and secure code review assessments. As a co-founder of Puma Security, his passion lies in modern static analysis product development and DevSecOps automation.